In today’s digital landscape, organizations face increasingly complex and evolving cybersecurity threats. Traditional security information and event management (SIEM) systems often struggle to provide real-time threat intelligence, scalability, and cost-effectiveness. Microsoft Azure Sentinel, a cloud-native SIEM and security orchestration automated response (SOAR) solution, addresses these challenges by leveraging artificial intelligence, automation, and the power of the cloud. Deploying Azure Sentinel effectively requires a structured approach, from initial planning to integration and continuous optimization.
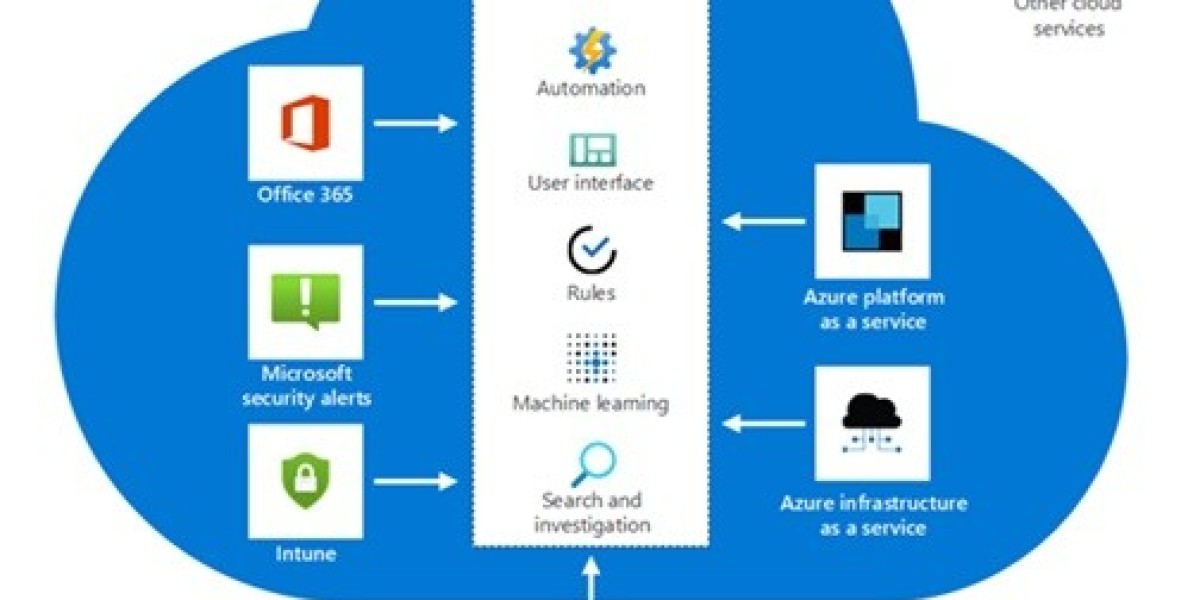
Azure Sentinel provides a single solution for threat detection, investigation, and response. Unlike on-premises SIEM tools, it eliminates infrastructure management overhead and scales automatically based on organizational needs. It integrates seamlessly with Microsoft services such as Microsoft 365 Defender, Azure Active Directory, and third-party solutions, enabling security teams to gain end-to-end visibility across hybrid and multi-cloud environments.
Before deploying Azure Sentinel, organizations should perform a detailed readiness assessment. This includes evaluating current security posture, data sources, compliance requirements, and available expertise. Key questions to address include:
What are the critical systems and data sources to monitor?
What compliance frameworks (e.g., GDPR, HIPAA, ISO 27001) must be supported?
What is the expected scale of data ingestion, and how will costs be managed?
A clear roadmap ensures that the deployment aligns with business and security goals.
Deployment begins by provisioning Microsoft Azure Sentinel Deployment through the Azure portal. Since Sentinel is built on top of Azure Log Analytics, creating a Log Analytics workspace is the first step. Organizations should design a workspace strategy that accounts for geography, data residency requirements, and role-based access control.
Next, data connectors must be enabled. Azure Sentinel provides native connectors for Microsoft services like Office 365, Azure AD, and Defender for Endpoint. Additionally, organizations can connect non-Microsoft data sources using built-in connectors or custom log ingestion methods via APIs and Syslog. Prioritizing high-value sources ensures maximum visibility from the start.
Once data flows into Sentinel, analytics rules are configured to detect threats. These rules leverage Kusto Query Language (KQL) to identify anomalies, malicious activities, or suspicious user behaviors. Microsoft provides pre-built rule templates that can be customized for organizational needs.
Visualization is essential for effective monitoring. Workbooks and dashboards provide real-time insights into security metrics, trends, and incidents. Customizing these dashboards helps align monitoring with business priorities and compliance reporting.
Sentinel integrates with Azure Logic Apps to create playbooks that automate responses to security incidents. For example, a playbook can automatically disable a compromised user account, block an IP address, or notify the security team via email or Teams. Automation reduces response time and allows security analysts to focus on complex threats.
The incident management feature consolidates alerts into actionable incidents. Security analysts can investigate incidents using built-in hunting queries or create custom queries for proactive threat hunting. This continuous approach helps uncover hidden threats and strengthens defense mechanisms.
Start Small, Then Scale: Begin by integrating critical data sources, test rules, and dashboards, then gradually expand.
Optimize Costs: Use data retention policies, archival storage, and selective log ingestion to manage costs effectively.
Leverage Threat Intelligence: Integrate Microsoft Threat Intelligence and third-party feeds to enhance detection accuracy.
Enable Role-Based Access Control: Assign appropriate permissions to ensure data security and compliance.
Continuous Improvement: Regularly review rules, playbooks, and dashboards to adapt to evolving threats.
A successful deployment transforms the organization’s security operations. Benefits include:
Scalability: Easily scales with growing data volumes without hardware limitations.
AI-Powered Detection: Machine learning models enhance detection of sophisticated threats.
Reduced Response Time: Automation ensures faster incident containment.
Cost Efficiency: Pay-as-you-go pricing minimizes upfront investments.
Unified Security Management: Centralized visibility across hybrid and multi-cloud environments.
Deploying Microsoft Azure Sentinel Deployment empowers organizations to move from reactive to proactive security operations. Its cloud-native architecture, combined with AI-driven analytics and automation, makes it a powerful solution for modern threat detection and response. With proper planning, phased implementation, and continuous optimization, Azure Sentinel becomes not just a SIEM platform but a strategic enabler of intelligent cybersecurity.